ESET
Multilayered business protection
advanced cloud security
ESET delivers comprehensive IT security solutions for businesses around the world, offering a safer technology space for everyone to enjoy and make the most of. Every day ESET products protect the data of millions of users across 180 countries worldwide, helping them use and explore the internet with confidence.
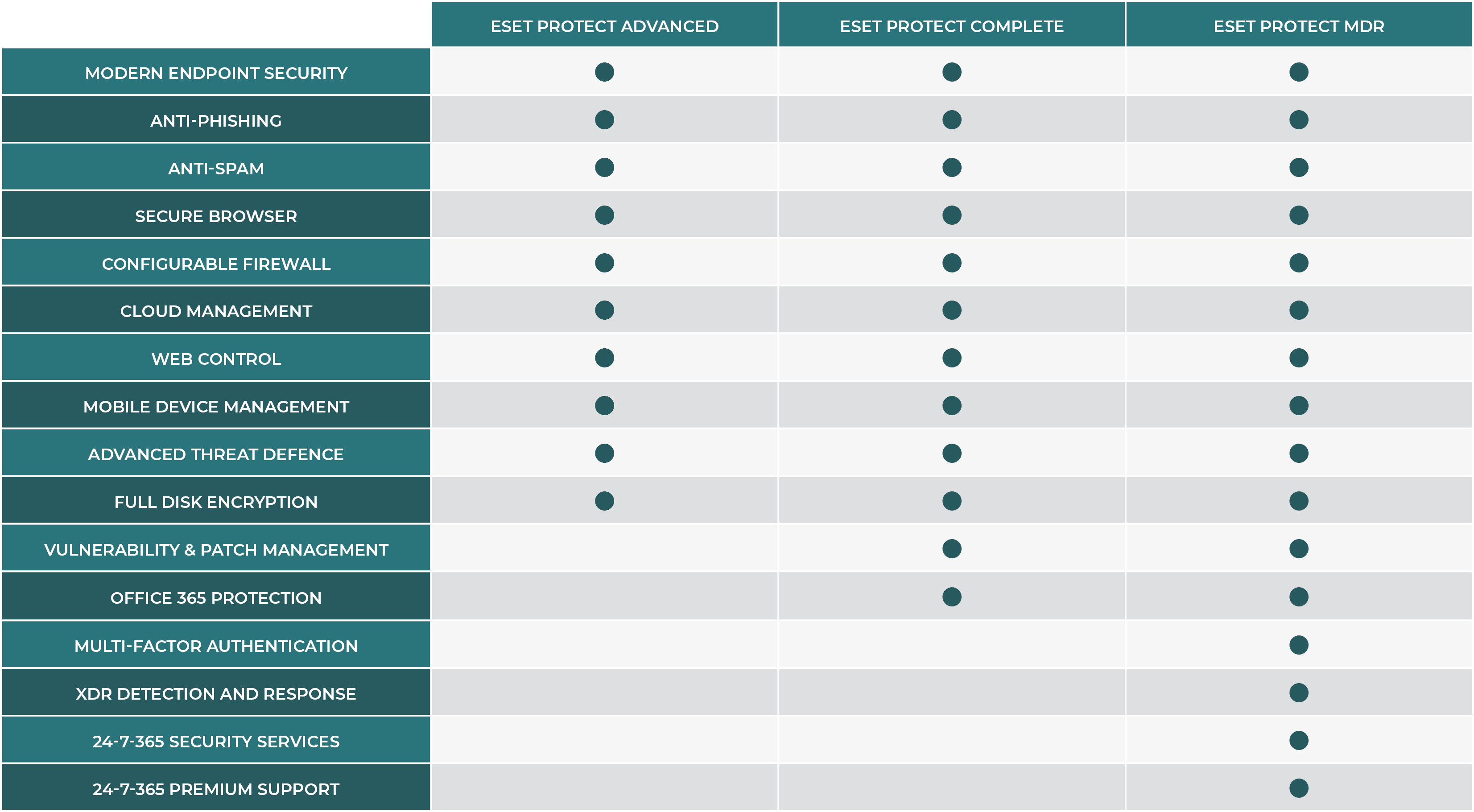
ESET Protect
Protect your business from cyber attacks, ensuring that your company endpoints, business data and users are secured with ESET’s multilayered technology. ESET PROTECT platform offers customisable security solutions, easy to manage from a Cloud console.
Endpoint Protection
··························································
Advanced multilayered protection for computers, smartphones and virtual
machines.
File Server Security
··················································
Real-time protection for your
company’s data passing through
all general servers.
Full Disk Encryption
·····················································
Robust encryption solution for system disks, partitions or entire devices to achieve legal compliance.
Management Console
Unified security management platform
providing superior network
visibility. Available as Cloud or
on-prem deployment.
Advanced Threat Defence
··························································
Proactive Cloud-based defence against
zero-day and never-before-seen
threat types.
Mail Security
··················································
Blocks all spam and malware
at server level, before they reach
users’ mailboxes.
Cloud app Protection
·····················································
Advanced protection for Microsoft 365
apps, with added proactive threat defence. Dedicated console included.
Scalable & customisable cybersecurity
To keep you one step ahead of any threat
Cross-platform
solutions
UK-based
customer care
Signature light
footprint
Easy deployment
Top-rated
malware detection
ESET Endpoint Protection
ESET Endpoint Protection Platform is a security solution deployed on company devices to prevent cyber attacks, detect malicious activity and provide instant remediation capabilities. Endpoint Protection comes as part of ESET Protect.
Managed from a unified console
All ESET endpoints, including mobiles, can be managed from our Cloud-based unified management console ESET PROTECT.
Stop fileless attacks
ESET endpoint protection platforms have mitigations in place to detect malformed or hijacked applications, protecting against fileless attacks.
Block targeted attacks
ESET’s endpoint protection solutions use threat intelligence information based on their global presence to prioritise and effectively block the latest threats, prior to their delivery anywhere else in the world.
Brute Force Attack Protection
Detects and blocks automated attacks that try to use password guessing techniques to gain access to your network.
Network Attack Protection
ESET Network Attack Protection improves detection of known network security vulnerabilities.
Botnet Protection
ESET Botnet Protection detects malicious communication used by botnets, whilst simultaneously identifying the offending processes.
In-product Sandbox
ESET’s in-product Sandbox assists in identifying the real behavior hidden underneath the surface of hidden malware.
Behavioural Detection - HIPS
ESET’s Host-based Intrusion Prevention System (HIPS) monitors system activity and uses a pre-defined set of rules to recognise and stop suspicious system behaviour.
Ransomware Shield
An additional layer protecting users from ransomware. Our technology monitors and evaluates all executed applications based on their behaviour and reputation. It is designed to detect and block processes that resemble ransomware behaviour.
Advanced Memory Scanner
ESET Advanced Memory Scanner monitors the behaviour of a malicious process and scans it once it decloaks in memory. Fileless malware operates without needing persistent components in the file system that can be detected conventionally. Only memory scanning can successfully discover and stop such malicious attacks.
UEFI Scanner
ESET is the first endpoint security provider to add a dedicated layer into its solution that protects the Unified Extensible Firmware Interface (UEFI). ESET UEFI Scanner checks and enforces the preboot environment’s security and is designed to monitor the integrity of the firmware. If modification is detected, it notifies the user.
Exploit Blocker
ESET Exploit Blocker monitors typically exploitable applications (browsers, document readers, email clients, Flash, Java and more), and instead of just aiming at particular CVE identifiers, it focuses on exploitation techniques. When triggered, the threat is blocked immediately on the machine.
Further Information
For everything you need to know about ESET and full access to our Resource Centre please click the button below
ESET Enquiry
Complete the form, press send and your enquiry will be directed straight to a member of the team.
Shortly afterwards, we will be in touch to discuss your requirements and answer any questions you may have.